Published 2026-01-19
Hey, have you ever had this experience? A certain microservice suddenly "loses its temper" and either gets stuck here or lacks permission there. As a result, the entire application falls down one after another like dominoes. What's worse is that you don't even know where the problem is, and you can only look for that little authorization setting like a needle in a haystack among hundreds or thousands of services.
This situation is actually very common. Imagine you build a skyscraper, but each room is assigned a different key, and the keys are managed in various ways - some rooms have password locks, some require swiping a card, and some even only recognize faces. Over time, who can still remember which room uses which rules? Authorization management in microservice architecture is a bit like this situation. Each service may manage its own set of permission logic. As a result, the system becomes more and more complex and difficult to maintain, and the seeds of security vulnerabilities are quietly planted.
Ask yourself a few questions first: Is each of your microservices repeating "inventing the wheel" and writing its own set of permission verification? When a new service is added, do we have to reorganize the entire permission chain, for fear of missing any link? Will changing a permissions rule trigger a series of unexpected crashes?
If the answer is "yes," then your system may be slowly being bogged down by authorization issues. A good authorization design should not place a heavier burden on each service, but make permission management clear and unified without disturbing the operation of the service itself.
Here are a few down-to-earth ideas:
You can think of a microservice system as a modern community. The authorization service is like the smart access control center of the community. When residents (users) enter the community, the access control center confirms their identities (authentication). When a resident wants to enter a certain building or use the gym (access a certain microservice), the building's card reader (service) does not need to store the permission list of all residents - it only needs to quickly ask the access control center: "Does resident A have the right to enter Building 3?" The access control center instantly checks resident A's property certificate, lease or visitor reservation (policy), and then replies "allow" or "deny".
In this way, the security system (microservice) of each building becomes very simple, and only needs to know "query" and "execution result". When a swimming pool (new service) is added to the community, or visitor rules are modified, only the access control center policy needs to be updated, without having to modify the system of each building.
There are tools and frameworks on the market that claim to solve these problems. But before making a decision, you might as well consider it from several practical angles:
Choosing technology can sometimes be a lot like choosing everyday tools. You don't always need the one with the most functions and the coolest, but the one that's most handy and least likely to cause trouble for you. A good microservice authorization solution should make you "not feel its existence" most of the time - it works quietly and reliably, and only clearly tells you "ok" or "no" when it is really needed.
It should help your team free up their energy from the tedious work of stitching permissions and refocus on building core business functionality. After all, the security of the system should not be based on the engineers' always tense nerves.
Ultimately, the goal of delegation management is not to build an ironclad wall but to establish order and clarity. Let data flow securely to the right people and systems at the right time, in the right way. When each microservice only needs to care about what it is best at, the entire system will be full of simplicity and efficiency.
On this road, likekpowerThe value of such partners who focus on providing underlying stability is often reflected in this: when you almost forget about authorization management, it just means that they have done their job well. Good technical solutions ultimately serve people and make creation smoother, rather than setting up new obstacles.
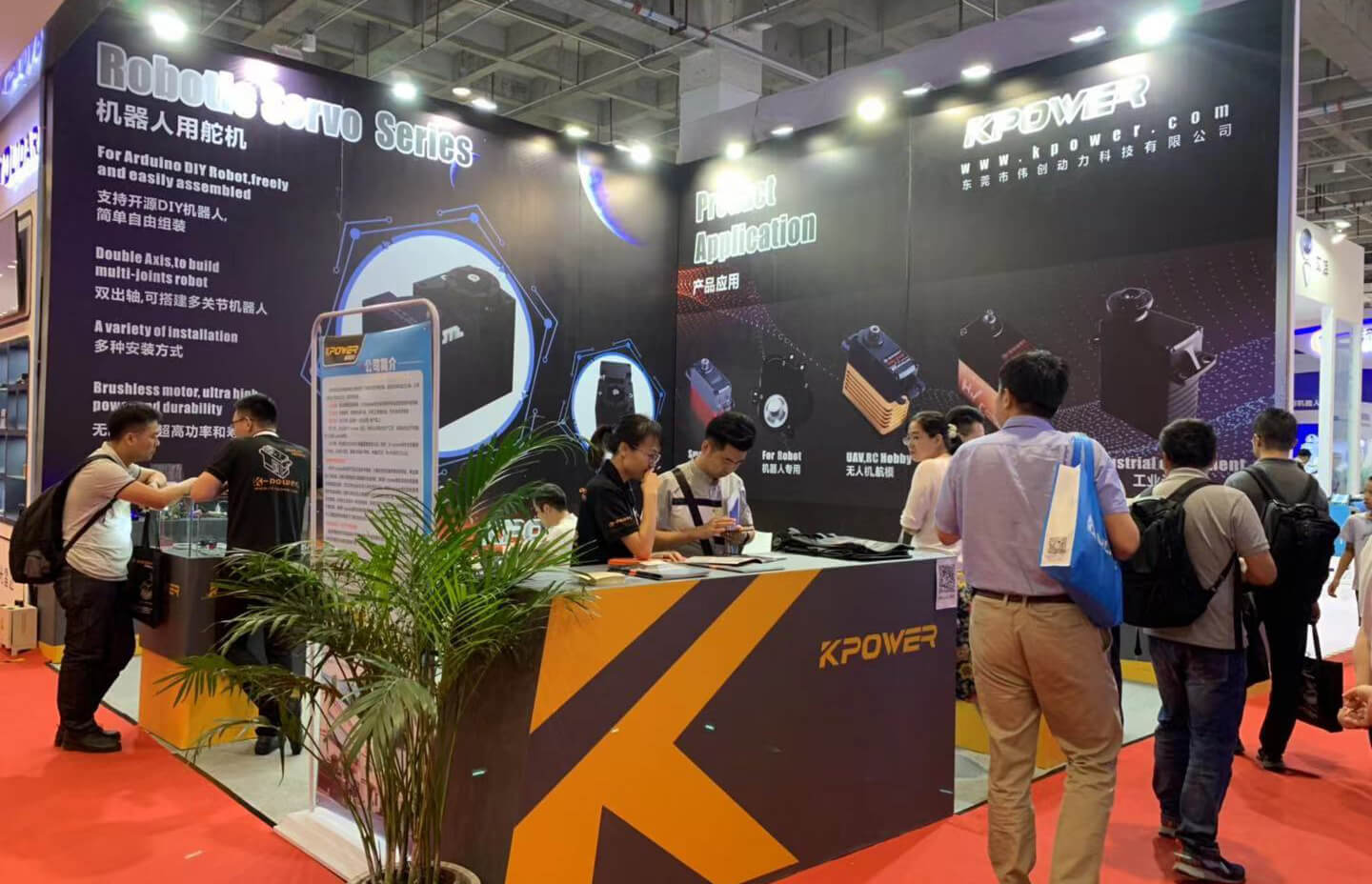
Established in 2005,kpowerhas been dedicated to a professional compact motion unit manufacturer, headquartered in Dongguan, Guangdong Province, China. Leveraging innovations in modular drive technology,kpowerintegrates high-performance motors, precision reducers, and multi-protocol control systems to provide efficient and customized smart drive system solutions. Kpower has delivered professional drive system solutions to over 500 enterprise clients globally with products covering various fields such as Smart Home Systems, Automatic Electronics, Robotics, Precision Agriculture, Drones, and Industrial Automation.
Update Time:2026-01-19
Contact Kpower's product specialist to recommend suitable motor or gearbox for your product.